
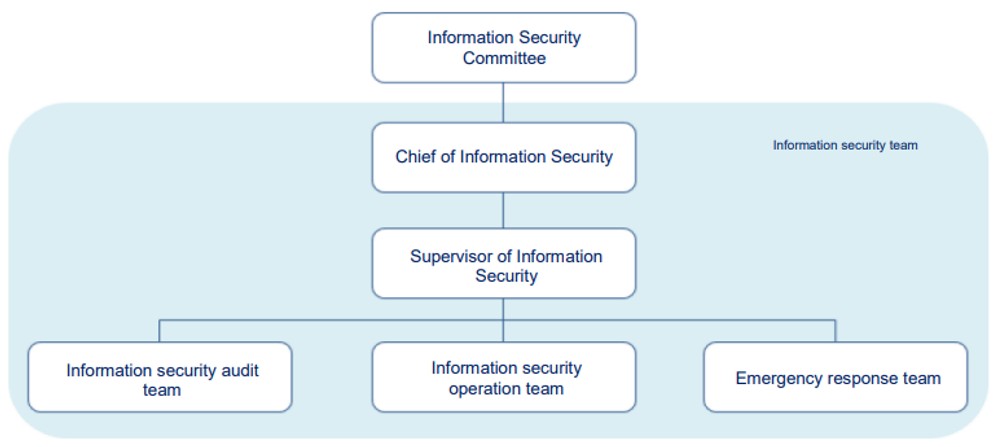
Management organization
To enhance the company's information security management and ensure the security of data, systems, and networks, an Information Security Management Committee has been established. The Chief Information Security Officer (CISO) serves as the convener of the Information Security Task Force and reports to the Board of Directors at least once a year. The CISO has reported to the Board on November 11, 2025.
The organizational structure consists of the Security Operations Team, the Incident Response Team, and the Security Audit Team:
-The Security Operations Team is responsible for implementing information security systems, including network and system management.
-The Incident Response Team is in charge of business continuity planning and crisis management procedures, executing emergency response measures, incident reporting, post-incident analysis, and preventive actions.
-The Security Audit Team collaborates with the company's audit unit to conduct information security audits, including internal and external audits.
Information security policy
The company's information security policy aims to "maintain the confidentiality, integrity, availability, and legality of company information, and avoid human negligence, deliberate destruction, and natural disasters, which result in improper use, leakage, tampering, damage, or disappearance of information and assets which affect the company's operations and cause damage to the company's rights and interests." The company introduced the ISO27001 information management system in 2016, and has regularly obtained ISO27001 certification. The current certificate is valid from August 2025 to August 2028.
Through the introduction of the ISO27001 information security management system, the ability to respond to information security incidents has been strengthened, and assets of the company and customers are more secure.
Information Security Risk Management Mechanism
|
Item
|
Specific management measures
|
| Information Security Team |
The team, composed of 19 representatives from various functions, is responsible for promoting and maintaining information security. Information security-related meetings are held at least once per quarter. |
|
Firewall protection
|
1. Set firewall connection rules.
2. Can only be opened with the approval of the responsible supervisor when there are special connection needs.
|
|
User Internet access control mechanism
|
1. Use an automatic website protection system to control users' online behavior.
2. Automatically filter users' Internet access to websites that may have links to Trojans, ransomware, or malicious programs.
|
|
Antivirus software
|
Use antivirus software and automatically update virus pattern files to reduce the chance of infection.
|
|
Updating of the operating system
|
The operating system is automatically updated. If it is not updated for some reason, the information center will assist in updating.
|
|
Email security control
|
1. There is automatic email threat scanning protection that prevents suspicious attachment files, phishing emails, spam emails, and expands the protection range against malicious links before users receive emails.
2. After a personal computer receives an email, the antivirus software also scans it for suspicious attachment files.
|
|
Data backup mechanism
|
Every important information system database is set up for daily backup.
|
|
Important file upload server
|
The important files of each department in the company are stored on this server, which is backed up and saved by the information center.
|
| Network Transmission Protection |
1.Encryption of connection channels.
2.Data content encryption and digital signature verification.
|
| Data Preservation Protection |
1.Dynamic Data Masking: Only authorized data can be accessed.
2.Content Encryption Storage: Sensitive data is encrypted before being stored in the database and must be decrypted for use. |
|
Cyber Insurance
|
Our company primarily serves corporate clients and does not face risks related to the storage of sensitive consumer data. After evaluating the coverage and applicable industries of available cyber insurance policies, we have decided not to purchase cyber insurance at this time.
To address cybersecurity challenges, we continuously monitor trends in the evolving information security landscape and implement relevant software and hardware solutions, such as firewalls, antivirus programs, and intrusion prevention systems. Additionally, we enhance employees' awareness of cybersecurity risks and strengthen the incident response capabilities of our cybersecurity personnel.
|
Enhancement in Digital Information Security.Upgrade of Customer Privacy
In order to protect customer information, the Company has established a customer information management system, which focuses on organizational management and operation from the perspective of corporate strategy. Through the analysis of business procedures and information systems, the Company examines the access control of personal information acquisition, processing, transmission and storage, and discloses the privacy statement of customer information on the dealer’s website, which not only promises to protect customer privacy, but also clearly explains the use and security regulations of customer information to protect customer privacy. In 2024, the Company did not infringe customer privacy or received complaints by our customers on the infringement of their privacy.
Incident notification procedure
When an information security incident occurs, the unit(s) to which it occurred will notify the information security team— incident response team, determine the type of the incident, find the problem point, deal with it immediately, and leave a record.